Trojan Magnum Large Size Chart
Trojan Magnum Large Size Chart - Attackers can export files, modify data, and delete files on your device. Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. A rat gives the attacker complete control over the victim’s computer, effectively turning it into a tool for cybercriminals to exploit. Discover how trojans work and how to prevent trojan attacks and protect users. This means they either have to be downloaded manually or another malware needs to. A trojan is a sneaky type of malware that infiltrates devices by camouflaging as a harmless program. Trojans are a common type of malware, which, unlike viruses, can't spread on their own. A trojan horse virus is a type of malware that disguises itself within legitimate applications and software. Trojans are packaged and delivered inside. Trojans are hard to detect, even if you’re. Trojans are hard to detect, even if you’re. A trojan horse virus is a type of malware that disguises itself within legitimate applications and software. A trojan is a sneaky type of malware that infiltrates devices by camouflaging as a harmless program. Attackers can export files, modify data, and delete files on your device. Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. Trojans are a common type of malware, which, unlike viruses, can't spread on their own. Discover how trojans work and how to prevent trojan attacks and protect users. This means they either have to be downloaded manually or another malware needs to. Trojans are packaged and delivered inside. Learn how you can put up a strong defense against them. Trojans are packaged and delivered inside. A trojan horse virus is a type of malware that disguises itself within legitimate applications and software. This means they either have to be downloaded manually or another malware needs to. What is a trojan virus? Attackers can export files, modify data, and delete files on your device. This means they either have to be downloaded manually or another malware needs to. What is a trojan virus? Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. Educate yourself on how trojan horse viruses sneak onto your devices. A trojan horse (trojan) is a type of. Attackers can export files, modify data, and delete files on your device. A trojan horse (trojan) is a type of malware that disguises itself as legitimate code. A trojan horse virus is a type of malware that disguises itself within legitimate applications and software. Discover how trojans work and how to prevent trojan attacks and protect users. Trojans are hard. What is a trojan virus? A trojan horse virus is a type of malware that disguises itself within legitimate applications and software. Trojans are packaged and delivered inside. Educate yourself on how trojan horse viruses sneak onto your devices. This means they either have to be downloaded manually or another malware needs to. Trojans are packaged and delivered inside. Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. This means they either have to be downloaded manually or another malware needs to. What is a trojan virus? Learn how you can put up a strong defense against them. Attackers can export files, modify data, and delete files on your device. A trojan horse virus is a type of malware that disguises itself within legitimate applications and software. What is a trojan virus? Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. Trojans are a common. Educate yourself on how trojan horse viruses sneak onto your devices. Trojans are hard to detect, even if you’re. A trojan horse virus is a type of malware that disguises itself within legitimate applications and software. This means they either have to be downloaded manually or another malware needs to. A rat gives the attacker complete control over the victim’s. Trojans are hard to detect, even if you’re. Trojans are packaged and delivered inside. A trojan is a sneaky type of malware that infiltrates devices by camouflaging as a harmless program. A rat gives the attacker complete control over the victim’s computer, effectively turning it into a tool for cybercriminals to exploit. Trojan horse malware is a file, program, or. Trojans are hard to detect, even if you’re. Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. A trojan is a sneaky type of malware that infiltrates devices by camouflaging as a harmless program. Trojans are a common type of malware, which, unlike viruses, can't spread on. A trojan horse (trojan) is a type of malware that disguises itself as legitimate code. Trojans are a common type of malware, which, unlike viruses, can't spread on their own. Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. Discover how trojans work and how to prevent. Learn how you can put up a strong defense against them. A rat gives the attacker complete control over the victim’s computer, effectively turning it into a tool for cybercriminals to exploit. Trojan horse malware is a file, program, or piece of code that appears to be legitimate and safe, but is actually malware. Trojans are hard to detect, even if you’re. Attackers can export files, modify data, and delete files on your device. This means they either have to be downloaded manually or another malware needs to. Trojans are a common type of malware, which, unlike viruses, can't spread on their own. Discover how trojans work and how to prevent trojan attacks and protect users. What is a trojan virus? Trojans are packaged and delivered inside. A trojan horse virus is a type of malware that disguises itself within legitimate applications and software.Trojan Condom Size Chart Find your perfect condom infographic
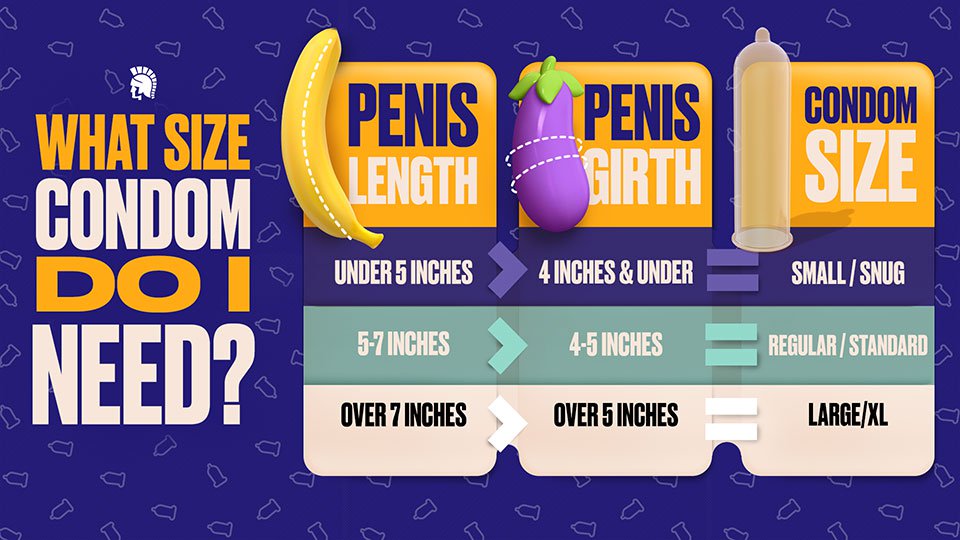
Trojan Condom Size Chart Find your perfect condom infographic
Trojan Condom Size Chart Find your perfect condom infographic
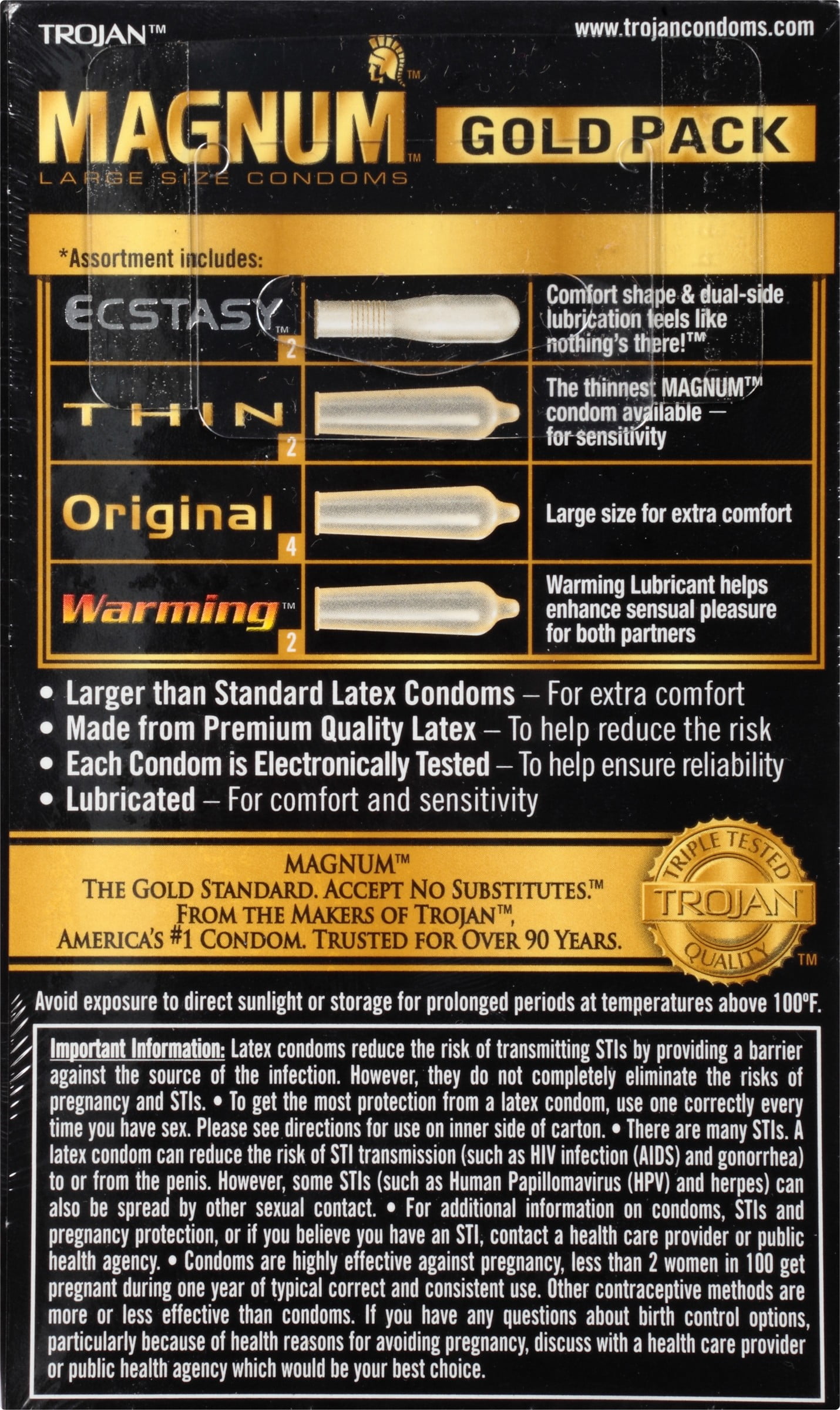
Trojan Magnum Xl Size Chart
Trojan Magnum Xl Size Chart
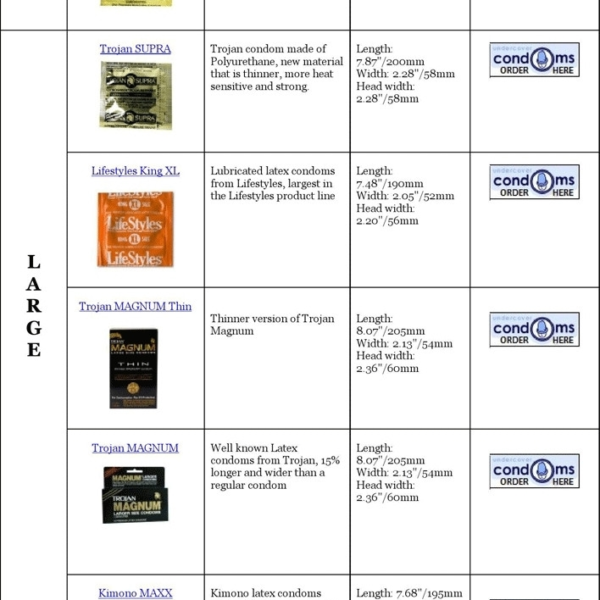
Trojan Condoms Size chart for each size and need
Trojan Condom Size Chart Find your perfect condom infographic
Trojan Condom Sizes Chart Condoms pasante regular naturelle mates flavours
Trojan Magnum Xl Size Chart
Trojan Magnum Xl Size Chart
A Trojan Is A Sneaky Type Of Malware That Infiltrates Devices By Camouflaging As A Harmless Program.
Educate Yourself On How Trojan Horse Viruses Sneak Onto Your Devices.
A Trojan Horse (Trojan) Is A Type Of Malware That Disguises Itself As Legitimate Code.
Related Post: